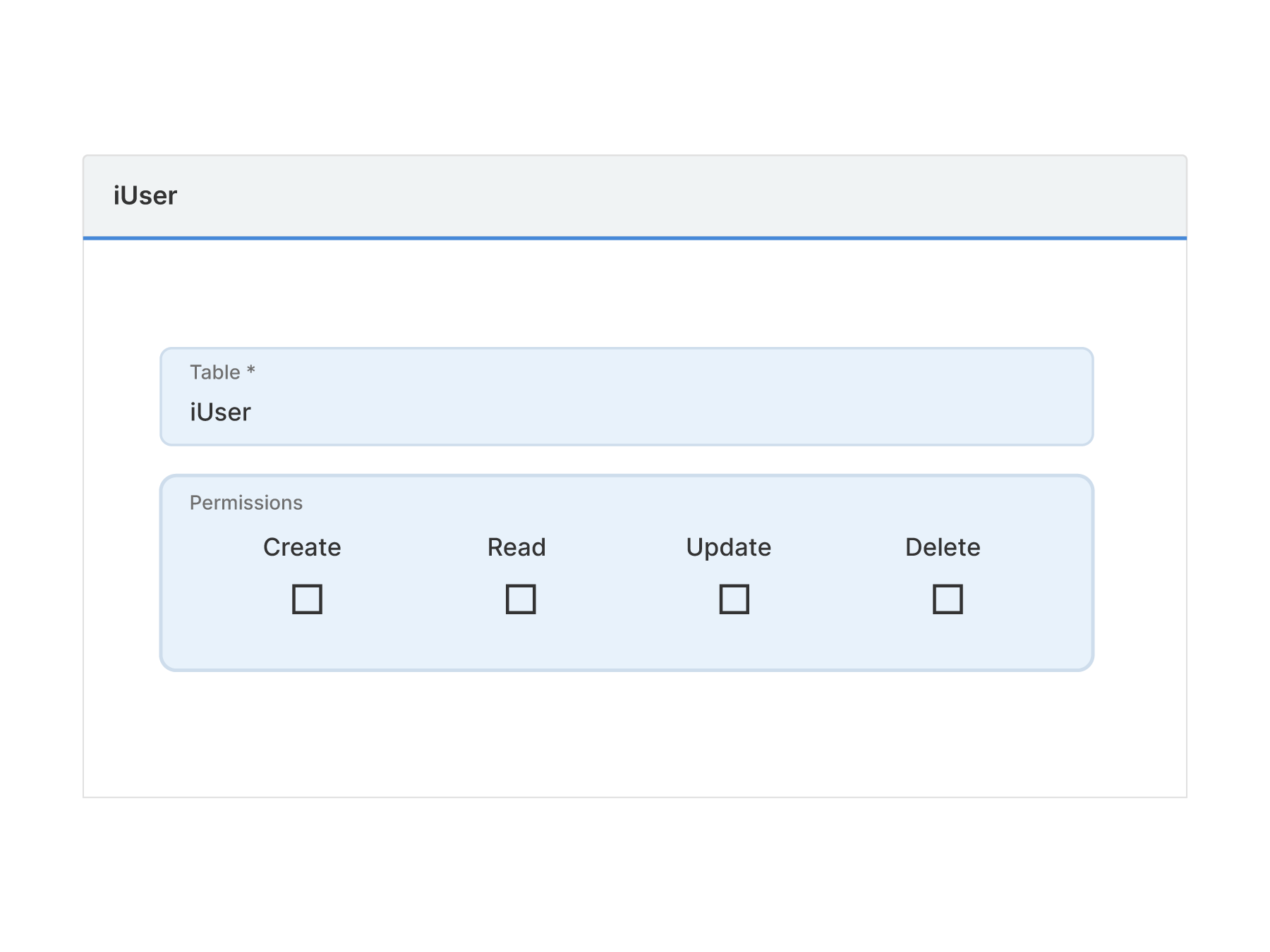
Implement Authentication and Create
User Roles By Assigning Permissions
Five gives developers the tools to implement authentication quickly, securely and easily.
Build applications for unlimited internal or external users (paid Team subscription or higher required).
Create CRUD permissions on the database, table, record or UI level.